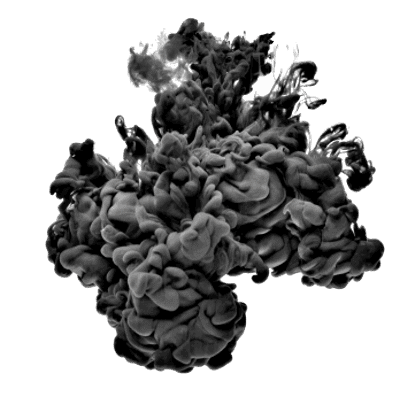
You are hopefully already covered with traditional security safeguards like firewalls, anti-virus, and anti-malware. While necessary, these platforms target only a portion of your cybersecurity defence by protecting the perimeter of your network from external threats.
But, did you know that most experts find that 70% of all breaches and threats originate inside the network, leaving you vulnerable where you might least expect!

The threat landscape has changed over the past few years; we had viruses, then malware, crypto viruses and now significant and repeated network & privacy breaches. Many industries now include mandatory reporting. Frequently small business IT teams are stretched thin, and in some cases, rely on outdated technology due to budgetary constraints.
Until now, you needed considerable investments to hire IT, security experts, expensive licensing deliver even the most basic IT security services. Our security scanning system changes all that. We run some nonintrusive data collectors on your network, then crunch the collected data to produce a set of IT security reports.
A typical network of 1-2 servers, 30 computers will take roughly 2-3 days to complete the review and gather a baseline.
Once completed, our reports provide actionable intelligence that will help you enhance your cybersecurity stance and reduce the risks of an attack. The reports deliver a baseline for the current state of your IT infrastructure and allow you to make informed business decisions about the ongoing effectiveness of your IT security posture.
Fill out the form on the right, and we will run a no obligation dark web scan for leaked passwords on your business domain. Let us know the size of your office, and we will provide an estimate for the scan/review.

We are so confident in the results, that if you are not satisfied, for any reason all fees and charges under the assessment are refundable.
Deliverables

(if supported)

tel:613 686 6263
Demand ITS has provided IT support to the Ottawa Region since 2006, we have clients in Montreal, Quebec City, Toronto, Kingston including the majority within the greater Ottawa area. If you’re looking to be sure about your IT security stance let us help you get the information you need to make a business decision.
[frontpage_news widget=”271″]